There have been taking place numerous types of cases with the help of emails. The emails some of the time contain messages from a friend, family, or work colleagues. The emails may seem right until you open the attachment and see what’s in it. If the email contains wrongly sent data in the attachment that can erase the data on the device you have open it. This will let the hacker have control over all your data. Even though your friends or anyone make you download a file or asks you to open a link then refuse him right there because it is expected that the link or the apps that you were going to download might be hacked by the hacker.
The hacked link can be found in various places instead of e-mail. You may not know which link or site or news feed or social networks are hacked and out of know where you end up at the unsafe website address and your data tend to get away from your hand. To prevent yourself from the data that gets away when you are hit with the attack, we here will see what it takes to prevent yourself from such a scenario.
How to identify the malicious site attack?
There are websites and apps created for getting fully sure about the site is a hack or not. This was an urgent need as the cases were increasing day by day and reaching the peak. This will create awareness to check if the website is safe or not. Here is the solution you can try to identify the site –
- Web (vms.drweb.com)
They are antivirus software developed for creating a wall of protection from threats. They protect users from phishing activity, viruses on the social network, blocking ads, ad network, ad-block on pages along with these they also practice the function such as –
- Verifies phishing, malware, and malicious website
- Verifies the downloaded files from the internet
- Verifies the site you follow on the internet
The website will help you get the answer to is this website safe.
- McAfee VirusScan (in/viruscan)
The renowned McAfee antivirus is developed for identification and for deflecting site threats. This is stated to be the most common antivirus software for identification. For identifying the virus go to the website that you assume contains the virus and copy the URL and paste it in the McAfee site verification bar to check if the website is safe or not. Within a second it will reflect the scan result and help you gain trust whether the site is safe or not. Website those are trustworthy gets 90% and dangerous one end up at 10% only.
- VirSCAN (org)
It is an online service that acts as a helping hand for verifying malicious and faulty files using multiple anti-virus inventions. Being the scanner is used online the files are verified in the browser itself. The scanner can verify 20 files at a time that are less than 20 MB.
Steps –
- Log in
- Click on select file
- Select the necessary file from the pop window.
- Select the scan button and it will start the scanning process
It may take some time but you will get it very soon.
- VirusTotal (com)
It is a renowned VirusTotal application that is brought by Google Inc in September 2012 fulfils the list. It is also one of the most preferred files checking online services. To check or scan the file the website uses 44 various antiviruses to see whether the file is up-o the mark or not. As the user downloads a particular file from a website it will go through analyses of a code to verify whether the file is safe and sound to go forward. With all the analyses done you will get the final report of the anti-virus products. The antivirus data is thoroughly updated with time intervals it helps out to verify the fresh and recent errors in the files or links, this is a great advantage for the user using the following web server.
Prevention
Be very transparent with the web page that uses the Socket layer or transport layer security and verify the server’s name pre-you type confidential information.
SSL is commonly used for helping to protect your information that travels all over the internet by encoding the following. It makes sure that the data that is being sent is going to the correct server. With the help of the SSL certificate, you can verify the name of the server that the page is based on. Make sure there is a lock sign at the start of the address bar.
For scanning, the server’s name that is being reflected on the certificate issued clicks on the lock icon and then verify that to whom the certificate is issued. The website doesn’t use SSL and if the lock sign doesn’t appear then it is not safe to send your personal information. If the name of the person to whom it is issued is different then shut the website and report it.
To be two feet away from the malicious website is preferable to prevent such an attack to get hit. Or else you manually type the URL of the given website in the address bar. With the following practice, you will come to know how does internet explorer loads the site. For doing the following –
- Type the websites URL in the address bar
- Press Enter
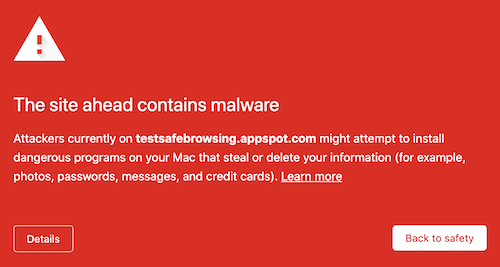
The malicious attack act very dangerous sometimes and they are represented in such a way –
– No SSL certificates
– Strange behavior on a legitimate site
– Unwanted download
– Unusual URL
– Security tools warning
You can also try the following steps –
- Keep your website updated – it is one of the most important tasks for keeping your site safe. If you have your website on WordPress then you should keep updating your site from WordPress themes, WordPress files, and WordPress plugins that you have installed. Having an outdated antivirus version will hold you in contempt and the vulnerabilities will keep in you the position you can get attack by.
- Secure your login page – the landing page for logging in must be very clear and protected. The hackers can make a similar one and make people login into the fake website. This will lead to data collection of the user and the hackers get access to the user website. The login page is what the attacker focuses on more importantly. It is a hearty recommendation from my end to look into the safety of your website’s login page and prevent it.
- Create regular back-ups of your site – backing-ups of all the users’ data that is stored or uploaded on the website turns out to be beneficial. Back-ups are taken when the site is already been hit with an attack but they have malware that battles and saves the website some time to back up.
- Install a security plugin – several other security plugins act as a helping hand and protect your site from getting hit by the attacker. You need a plugin to let them battle the attack for not getting your website infected.
Always be protected from malware is the most perfect and crucial part without taking it for granted. WordPress provides the best and the secured security foundation which turns out to be very simplistic. But once in a lifetime, your website will be open for vulnerabilities and that is what you should not take for granted.