To prevent tampering or compromise of applications by unauthorized parties, software developers digitally sign their programs with code signing certificates.
For software code or scripts, a code signing certificate is a digital certificate which serves to verify the authenticity and integrity of that software. It’s issued by a trusted Certificate Authority (CA), like SSl.com to a software developer or organization. The developer signs the code with a digital signature, and the certificate ties the code back to the developer’s identity and shows a user that the code is trustworthy and free from any subsequent changes to the code.
This digital certificate is only meant for signing code, and thus the Key Usage of Key Usage in PKI. There is also a time stamp recorded when we apply a digital signature to the code. This is because this signed code will still be valid after the digital certificate has expired. If no change or additions are made to the code, you don’t reapply a new signature until the original digital certificate that was used to sign expires.
What is Code Signing Certificate?
App stores and operating system providers expect secure code, and your customers do too, enforcing strict guidelines to make sure your app hasn’t been tampered with by third parties. SSL.com Code Signing Certificates are ideal for software developers and any organization striving to satisfy security needs. If you get your SSL.com code signing certificate subscription, you get cloud based secure private key storage or the high assurance Extended Validation (EV) needed for signing Microsoft Windows drivers.
Code Signing Certificates help you meet platform requirements, provide advanced protection for your organization, and avoid security warnings while your software is trusted with the highest level of digital security.
Signing authorization with Multi factor Authentication: Protect your code signing with two factor authentication (2FA) through the use of a USB token and manage your signing permissions with authorized only Hardware Security Module (HSM) certificate keys.
Identity Verification: Your identity verified, you can protect intellectual property and prevent tampering of code.
Timestamping: Secure with timestamps applied to certificates. It makes sure your signature is valid even after the certificate expired, since the signature expires, and re-signing is needed after the signature expires.
Integration Compatibility: Fast and easy to integrate throughout your code signing process across different platforms, from Authenticode to Kernel Mode and Paek of everything in between.
Buy Cheap Code Signing Certificate
Code Signing SSL certificates help publishers and software users to be sure that the files come directly from the publisher and are signed using a digital signature. We highly suggest not installing any software without author/published signature.
Why Code Signing Certificate?

Trusted on all versions of Windows

Displays “Signed by Your Company Name”

High assurance Organization Validated (OV)

30 Day Unconditional Refund

Prevents untrusted warning messages

Unlimited rekeys/reprocesses (for soft keys)
Benefits of Code Signing Certificates
Code Signing Certificates for Developers If you’re a software developer, whether an individual or an organization, publishing some code onto your website, SSL.com’s Code Signing Certificate is just for you. By utilizing the Code Signing Digital ID that has been made compatible with Microsoft Authenticode, your code stays protected, while eliminating the chance of someone tampering and making it look like yours. This certificate is a way to keep not only your code protected from them but also keep it authentic and intact.
Improves Customer Confidence: It builds trust with your users through proving that your code comes from a legitimate source. Enhances Software Downloads: It increases download rates by ensuring users they don’t get ‘stabbed’ with corrupt code. Establishes a Trusted Sales/Distribution Outlet: It empowers your software’s reputation and credibility in the market. Maintains Content Authenticity: Keeps your code intact, and true to its original state.
Ensures Software Accountability: Relieves you from fraud or abuse of the code makes it clear who owns the code. Windows Compatible: Being fully compatible with Windows operating systems, software is installed and used without any glitches.
Widely Recognized Certificate: Most browsers, platforms and security software recognized.
Code Signing Certificate to Secure All Your Code
Major software giants like Microsoft, JavaSoft, Adobe and Apple all trust code signing certificates across the industry. It provides an important layer of security to developers and organizations, confirming that the software they make use of is valid.
Advantages of Code Signing Certificate
Code signing carries the expression of the idea that digitally sign your software, programs, executables or applications to assure the authenticity and integrity of your software during download and installation. Here are the key advantages of using a code
Assurance & Authenticity
Digital Software Signature
Freeze Digital Signature
By timestamping your digital signature you ‘freeze’ it so even after your code signing certificates expires your signature is still valid. In doing so, the digital signature works appropriately and users are not affected.
Increased Software Sales
Unlimited Signing
You can sign any number of software files, executables and applications during the certificate is in force without paying extra charges. It enables you to buy several software releases at once without paying additional costs.
Software Integrity
You can sign your software by signing it with a code signing certificate (the correct file for that should be included in the installer), verify it with a hash function, guaranteeing them that the software is actually what was created, much like how you create your signed and sealed messages or contracts around the world. If the hash is different, i.e. depending on how the hash function was chosen, users will get a security warning that won’t let your software be downloaded or installed if tampered with.
Frequently Asked Questions about Code Signing Certificates
What is a Code Signing Certificate?
A code signing certificate is a digital document that verifies the identity of the publisher of a software program. It is similar to a physical signature on a document, but it is used to verify the authenticity of digital code. When you download a program from the internet, the code signing certificate tells you that the program is from a trusted source and has not been tampered with.
Why are Code Signing Certificates Required?
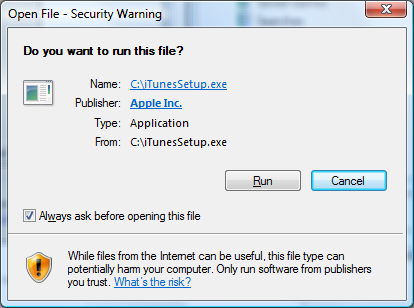
Code signing certificates are required by many software platforms, including Windows, macOS, iOS, and Android. When you try to install a program that is not signed, you will often be warned that the program may be unsafe. This is because unsigned programs can be used to install malware or steal your data.
Are there Different Types of Code Signing Certificates?
Yes, there are three main types of code signing certificates: individual, commercial, and extended validation (EV). Individual certificates are the most basic type and are suitable for small developers or hobbyists. Commercial certificates are for larger businesses and organizations. EV certificates are the most expensive type and offer the highest level of trust.
Can a Code Signing Certificate be Issued for Individuals?
Yes, individual code signing certificates are available for developers who want to sign their software for personal use or for distribution to a small group of users.
Why do I need a Code Signing Certificate?
There are several reasons why you might need a code signing certificate:
- To increase user trust: When users see that a program is signed, they are more likely to trust it. This can lead to increased adoption and sales of your software.
- To meet platform requirements: Many software platforms require programs to be signed before they can be installed.
- To protect your brand: A code signing certificate can help to protect your brand by ensuring that users know that your software is genuine.
How to remove Unknown Publisher error from software?
If you see an Unknown Publisher error when you try to install a program, it means that the program is not signed. You can try to fix this error by downloading the program from a trusted source or by purchasing a code signing certificate for the developer.
How much does code signing cost?
The cost of a code signing certificate varies depending on the type of certificate and the issuing authority. Individual certificates typically cost around $50 per year, while commercial certificates can cost hundreds or even thousands of dollars per year. EV certificates are the most expensive and can cost several thousand dollars per year.
What is the easiest way to get a code signing certificate?
The easiest way to get a code signing certificate is to purchase one from a trusted certificate authority (CA). There are many CAs to choose from, so it is important to compare prices and features before you buy.
What is EV code signing certificate?
An EV code signing certificate is the most expensive type of code signing certificate and offers the highest level of trust. EV certificates are issued by CAs after a rigorous vetting process that verifies the identity of the certificate applicant. EV certificates are typically used by large companies and organizations that want to ensure that their software is trusted by users.
Why is code signing certificate so expensive?
Code signing certificates are expensive because they require a significant investment from the issuing CA. CAs must maintain a high level of security and compliance in order to issue certificates. Additionally, CAs must invest in technology and personnel to verify the identity of certificate applicants.
Can I create my own code signing certificate?
Technically, yes, you can create your own code signing certificate. However, this is not recommended for most users. Creating your own certificate requires a high level of technical expertise and can be time-consuming. Additionally, self-signed certificates are not as widely trusted as certificates issued by CAs.